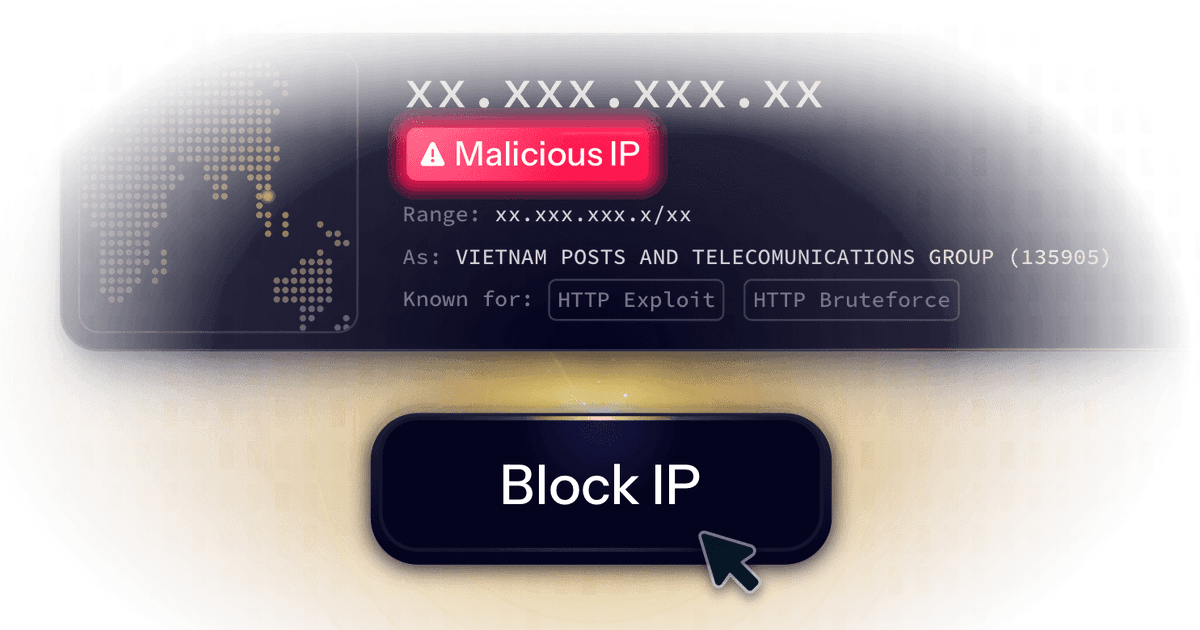
CrowdSec Intelligence Blocklist
Contains all IPs in our database that have been identified as actively aggressive, performing a wide variety of attacks. Proactively block these IPs if you don’t want to take any chances with malicious IPs potentially reaching your systems.