
Explore The Next Frontier in Cyber Threats and Defense Evolution!
Download ebook
Welcome to the CrowdSec Blog
Learn more about CrowdSec, our approach to tactical intelligence, and company news.









The Real Value of Preemptively Blocking a Cyber Attack
Preemptively blocking malicious IPs is not just good for your security posture, it’s also good for your wallet. In this article, I’ll explain how you can track remediation metrics using your CrowdSec Security Engine and how you can estimate the actual cost savings enabled by the CrowdSec Blocklists. Remediation Component metrics With the release of […]



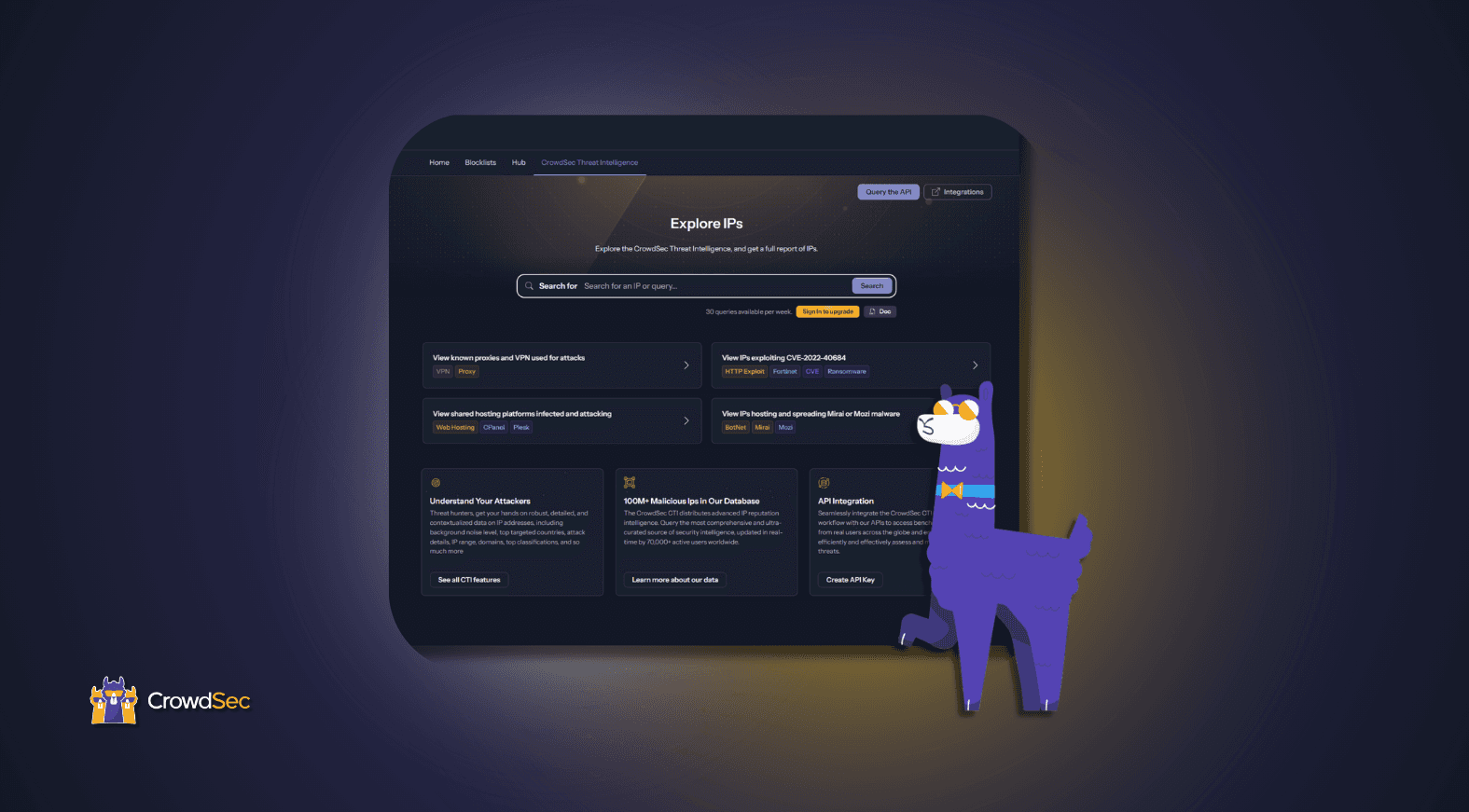
Introducing the New and Advanced IP Lookup Search
In a previous article, we introduced the CTI Report, this time, we are taking it a step further and introducing new and advanced search options for our IP lookup. You now have access to multiple search options to accurately and effectively explore the CrowdSec CTI. Let’s take a look. IP lookup search These new search […]